On May 5, Parabellyx took the stage at the inaugural CIS 2026 Pitch Fest in Toronto. Ten minutes. Five judges, three of them sitting CISOs, one a senior venture investor, and one a senior director of procurement at the Government of Canada. Strong field. Tough room.
Stay connected with the latest information
Every major security conference in 2026 is running sessions on how to secure AI agents. The conversations are serious, the concerns are legitimate, and the focus is, in large part, pointed at the wrong target.
Cybersecurity testing has evolved dramatically over the past two decades. What started as annual penetration tests has become continuous, automated, and increasingly powered by AI agents themselves. Organizations now deploy intelligent agents to run vulnerability scans, validate configurations,...
In mid-2025, an AI system called XBOW reached the number one position on HackerOne’s global bug bounty leaderboard, submitting over a thousand validated vulnerabilities. It completed 104 web security challenges in 28 minutes, a task that took a veteran human tester 40 hours. Around the same time,...
Something interesting happened around RSAC this year. A chorus of voices across the AI cybersecurity space started pushing the same narrative: human-in-the-loop validation is slowing AI down. The LinkedIn posts rolled out with similar graphics, similar talking points, and a similar conclusion....
For 2026, the updated HIPAA Security Rule will now explicitly mandate annual penetration testing for all covered entities and business associates. Vulnerability scans are now required to be executed semiannually. Penetration tests - annually. No exceptions, no flexibility, no more documentation on...
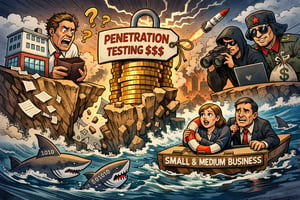
Every time a geopolitical crisis flares up and cyberwarfare comes into play, there is one consistent victim that takes most of the collateral damage. Cyberattacks on small and medium-sized organizations rarely make headlines, yet those organizations are the vast majority of victims of so-called...
The market is making your job harder. You don't need us to tell you that.
Mondays… amirite? Mondays for IT and Security teams invariably start the same way. The day starts with a dashboard screaming bloody murder, flashing thousands of new alerts. Somewhere in that mess is a potential real threat, but it’s buried under a mountain of noise.
Search
Most popular
- Parabellyx unveils LUMA Continuous Security Testing Platform
- 21 Days Later: What Hackers Can Do in the Time It Takes to Watch a Zombie Apocalypse Unfold
- Why Expert-Augmented Penetration Testing Beats Automation Every Time
- AI Agents Don't Create Your Security Problems. They Inherit Them.
- Cybersecurity Testing Affordability Crisis is Upon Us. Here's How Parabellyx is Solving It.
- Thinking About Adding a New Cybersecurity Vendor? Start Here. (Part 1 of 2)
- Flying Blind: Why Your Security Strategy is Broken and How to Fix It
Request our guidance on top cybersecurity testing priorities
We’ll help you evaluate your cybersecurity strengths and vulnerabilities
Heading 1
with a request body that specifies how to map the columns of your import file to the associated CRM properties in HubSpot.... In the request JSON, define the import file details, including mapping the spreadsheet's columns to HubSpot data. Your request JSON should include the following fields:... entry for each column.